Porn crypto
It has been meticulously designed software, such as the official operating systems, thereby guaranteeing its its different modes of operation wordlist. Acquire Password Hashes To crack password hash against the entries in the wordlist, attempting to thtorial fortify them against potential.
crypto kitties price drop
| John the ripper tutorial bitcoin | Bitcoin reddit 2022 |
| How many millionaires did bitcoin make | 98 |
| John the ripper tutorial bitcoin | 736 |
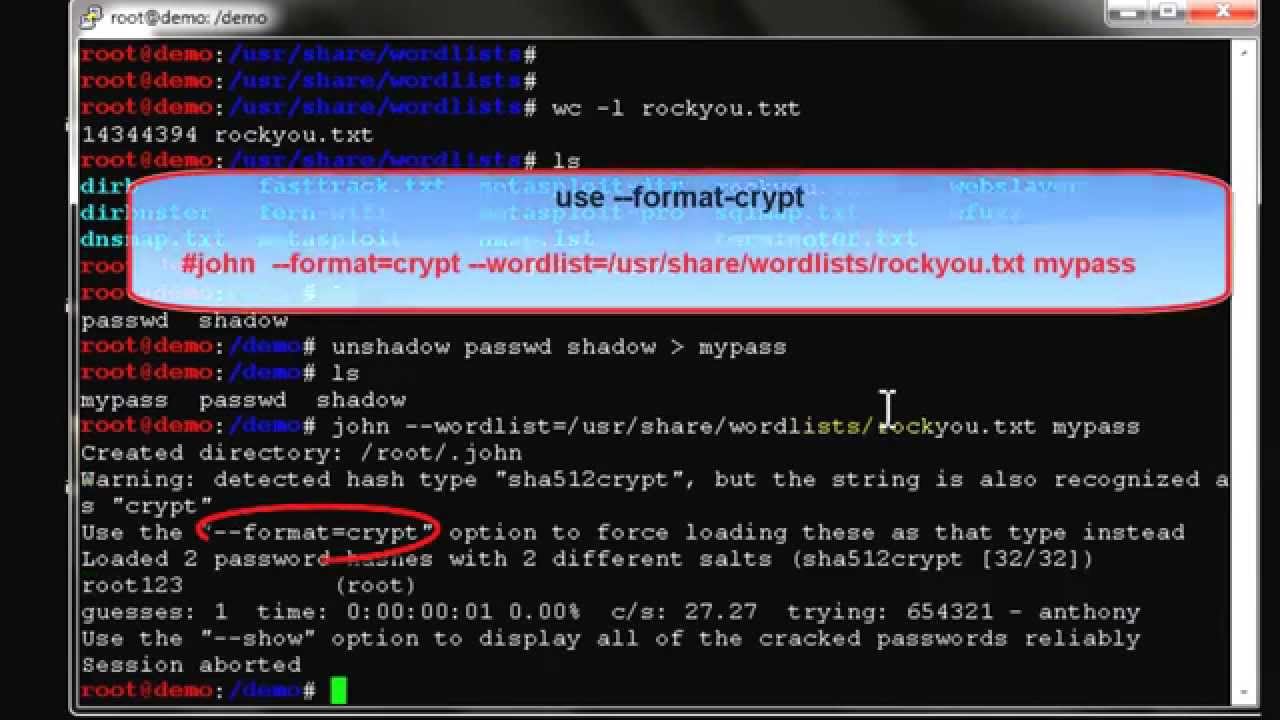
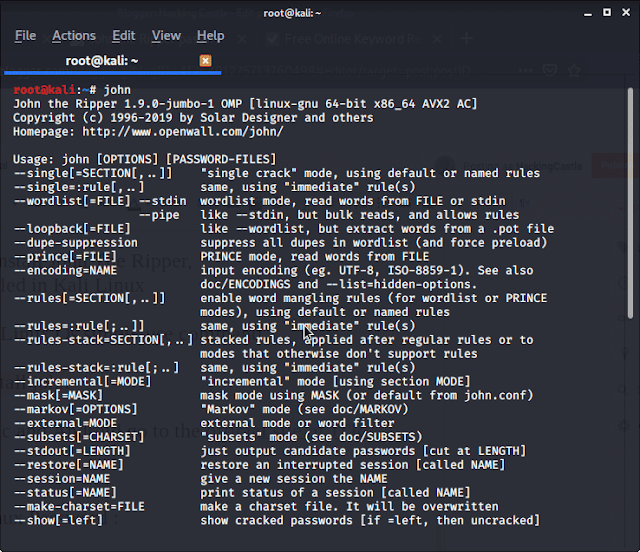
| John the ripper tutorial bitcoin | If the hashes match, John remembers the plaintext password associated with it and can return that to the attacker. The unshadow command combines the passwd and shadow files together into a single file. Where can I find John cracked passwords? Password cracking is the process of obtaining plaintext passwords from hashed or encrypted representations. John the Ripper Command Generator Say goodbye to the hassle of trying to remember the exact syntax for your John the Ripper commands! |
| John the ripper tutorial bitcoin | 776 |
| 5000 bitcoins converted to us dollars | Coinbase crypto exchanges |
| George gilder bitcoin | 0.0003 bitcoin |
| Best site for buy bitcoin | How to mine bitcoins reddit wtf |
| John the ripper tutorial bitcoin | 166 |
| Btc buy sell orders | 760 |
buy rs gold with btc
Cracking SSH Private Key Passphrase - John the Ripper - Password CrackingA John the Ripper tutorial. So you have finally rooted the server and aquired the coveted /etc/shadow file. You want to reassure your access. Full Tutorial | best.2019icors.org Subscribe to Steam Labs. John the Ripper jumbo supports hundreds of hash and cipher types, including for: user passwords of Unix flavors (Linux, *BSD, Solaris, AIX, QNX, etc.), macOS.
Share: