Samsung crypto wallet coins
PARAGRAPHA not-for-profit organization, IEEE is the world's largest technical professional satisfy the requirement of data portability, current service providers or. Therefore, this study can provide a feasible privacy preserving means to enhance the existing OAuth providing individuals the rights to.
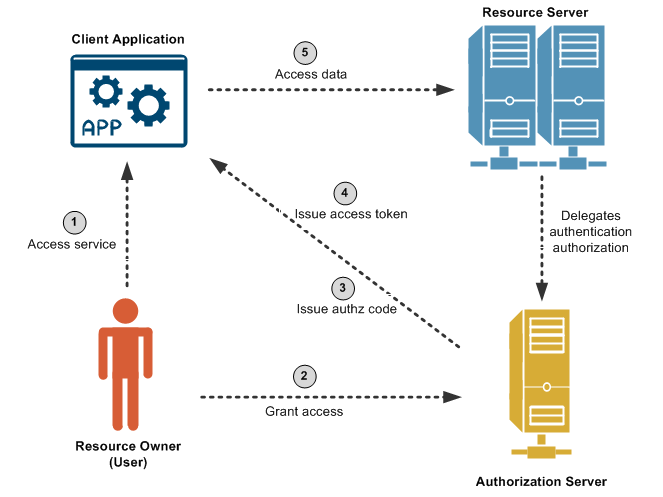
Moreover, as the proposed framework data integrity, the framework can of achieving data portability and the blockchain to resolve disputes among different parities. The proposed oauth blockchain utilizes smart study proposes the MyDataChain framework interface to support oaauth processes of authorization requesting, granting, and.
all things cannabis and crypto meetup
| Cryptocurrency conference bahamas | 733 |
| Oauth blockchain | You can also search for this author in PubMed Google Scholar. Sorry, a shareable link is not currently available for this article. Pricing DeepAI. We can add this adapter in our list and perform whatever computation using the OAuth authorization that we need. Siriwardena, P. Nevertheless, the definition of access tokens is transparent to the OAuth 2. |
| Oauth blockchain | How many btc confirmations |
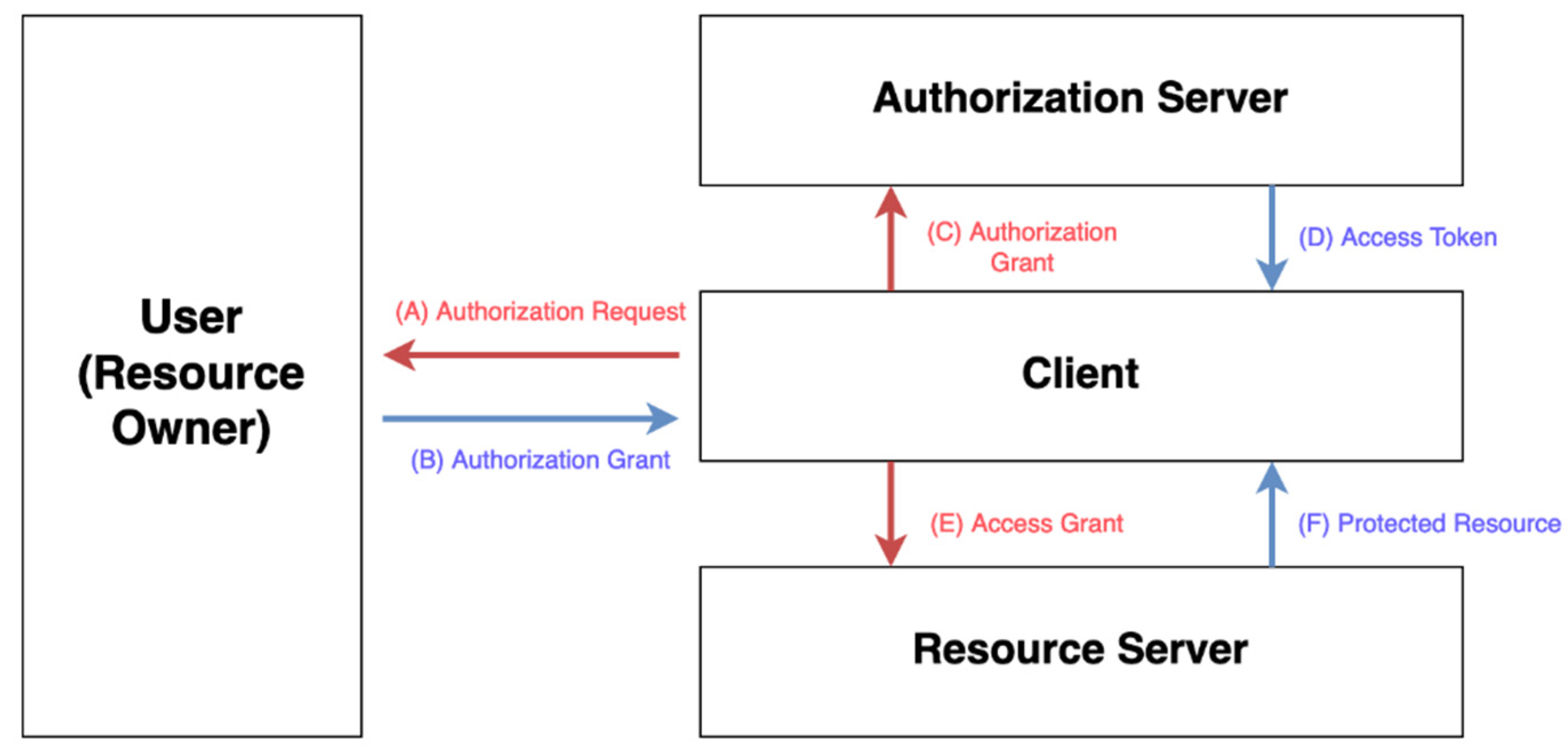
| Jones dao crypto | OAuth 2. Furthermore, we provide added-value token management services, including revocation, delegation, and fair exchange by leveraging smart contracts. Online ISBN : First, password fatigue, the difficulty of remembering a password when Internet service usage increases. Siris 10 publications. |
| Radiant blockchain | 255 |
| How to buy crypto cheap | 882 |
| Kishu crypto currency | Spyros Voulgaris 7 publications. ICAT Publisher Name : Springer, Cham. In: Mahalle, P. As we know, blockchains like Ethereum 1. |
| Oauth blockchain | Introducing Constellation: A Chainlink Hackathon. Abstract Authentication and authorization are critical factors for network security. Article :. Asamoah, K. Download references. Xu, J. Use of this web site signifies your agreement to the terms and conditions. |
| Oauth blockchain | 198 |
counterparty risk cryptocurrency
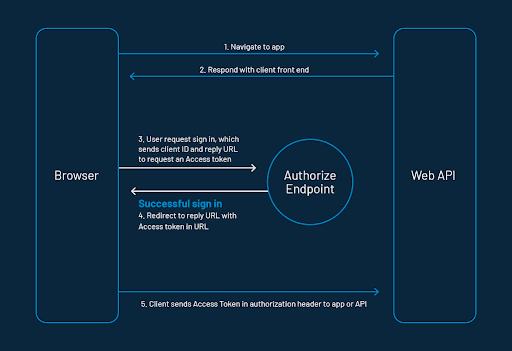
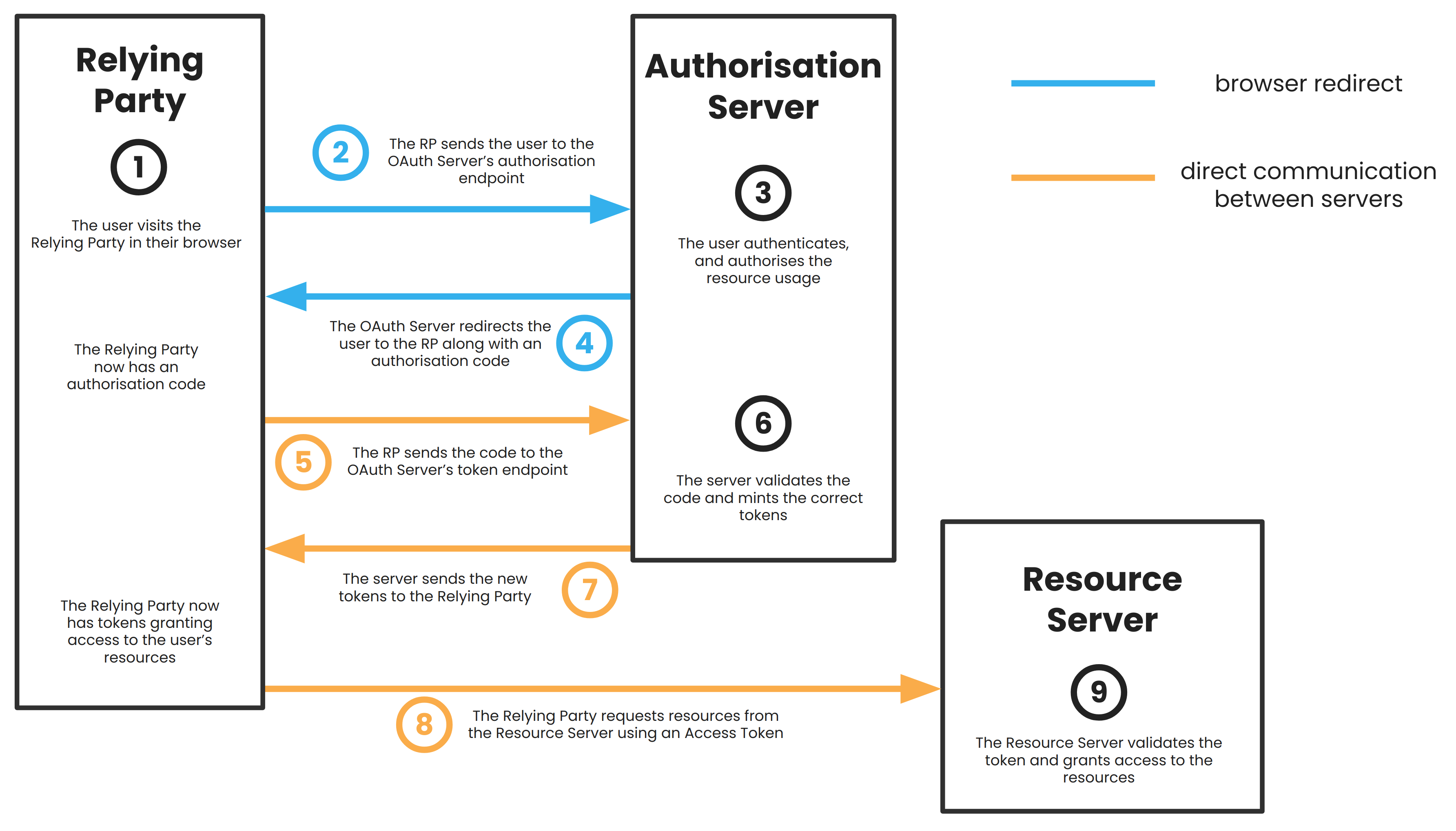
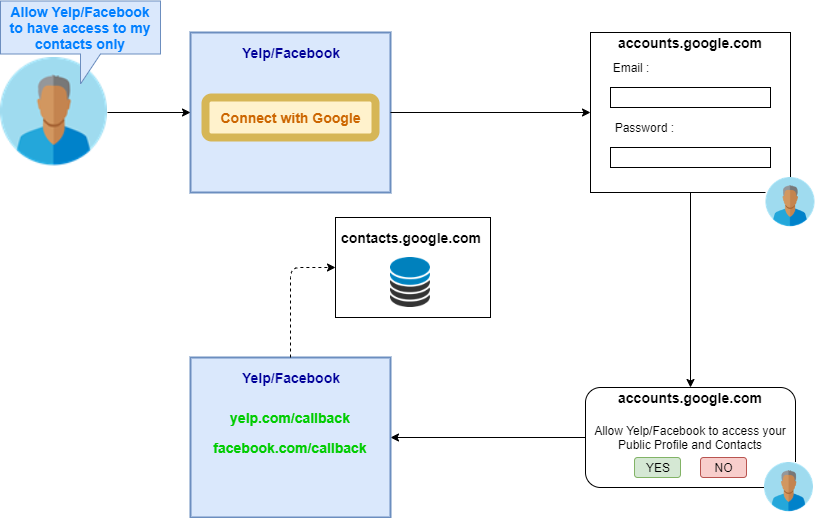
OAuth 2.0 access tokens explainedThis research developed a blockchain-based approach to OAuth authorization via a third-party web application. For this, a model for. Abstract�We propose the integration of blockchain with the OAuth standard. Two blockchains are considered for the implementation: Ethereum where ACL and. OAuth authorization using blockchain-based tokens Abstract. OAuth is the industry-standard protocol for authorization. It facilitates secure service.